Zscaler Annual IoT Report Identifies Shift in Shadow IoT Behavior Threatening Enterprise Security Posture
1,500 Percent Increase in IoT Traffic Through the Zscaler Cloud Highlights Dangerous Rise in Unauthorized Devices Brought into the Workplace
This press release features multimedia. View the full release here: https://www.businesswire.com/news/home/20200225005401/en/
(Graphic: Business Wire)
Organizations around the world are observing this Shadow IoT phenomenon, where employees are bringing unauthorized devices into the enterprise. With this onslaught of unknown and unauthorized devices, IT and security teams often won’t know these devices are on the corporate network nor how they impact an organization’s overall security posture.
Key Findings:
-
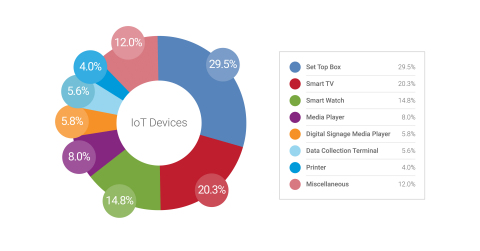
Unauthorized IoT Devices on the Rise: The top unauthorized IoT devices
Zscaler observed include digital home assistants, TV set-top boxes, IP cameras, smart home devices, smart TVs, smart watches, and even automotive multimedia systems. - Manufacturing & Retail Industries Top IoT Traffic Volume: Manufacturing and retail customers generated the highest IoT traffic volume (56.8%) followed by enterprises (23.7%), entertainment and home automation (15.7%), and healthcare (3.8%).
- Majority of IoT Transactions are Insecure: 83 percent of IoT-based transactions are occurring over plain-text channels, whereas only 17 percent are using secure (SSL) channels.
-
Exponential Increase of IoT Malware:
Zscaler blocked 14,000 IoT-based malware attempts per month. That number has increased more than seven times than theMay 2019 research. - New Exploits Emerging to Target Unauthorized Devices: New exploits that target IoT devices are popping up all the time, such as the RIFT botnet, which looks for vulnerabilities in network cameras, IP cameras, DVRs, and home routers.
“We have entered a new age of IoT device usage within the enterprise. Employees are exposing enterprises to a large swath of threats by using personal devices, accessing home devices, and monitoring personal entities through corporate networks,” said Deepen Desai, Vice President of
Over the quarter,
In response to the growing threat posed by Shadow IoT devices brought into the enterprise, IT organizations must first be able to gain visibility into the existence of unauthorized IoT devices that are already inside the network. Organizations should be considering a
To download the IoT Devices in the Enterprise 2020: Shadow IoT Threat Emerges report, please visit: https://info.zscaler.com/resources-industry-iot-in-the-enterprise.
About
Zscaler™, Zscaler Internet Access™, and Zscaler Private Access™, ZIA™ and ZPA™ are either (i) registered trademarks or service marks or (ii) trademarks or service marks of
View source version on businesswire.com: https://www.businesswire.com/news/home/20200225005401/en/
Vice President,
press@zscaler.com
Source:
Tom Stilwell
Vice President, Global Communications
press@zscaler.com
